IT Virtualization Essentials
Cheatsheet Content
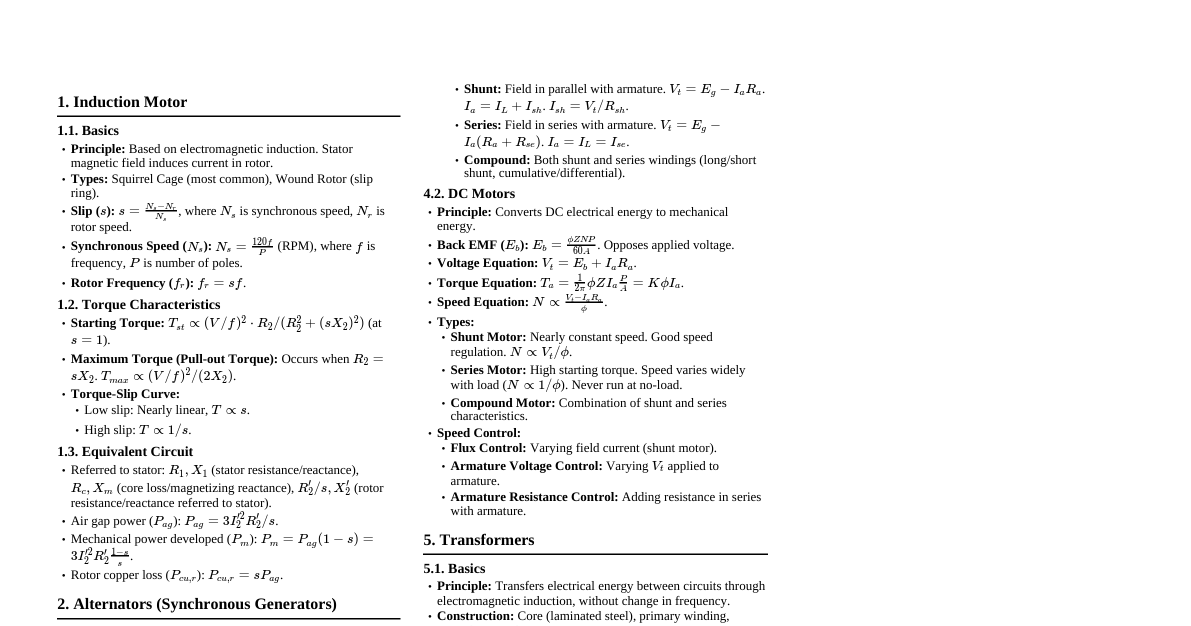
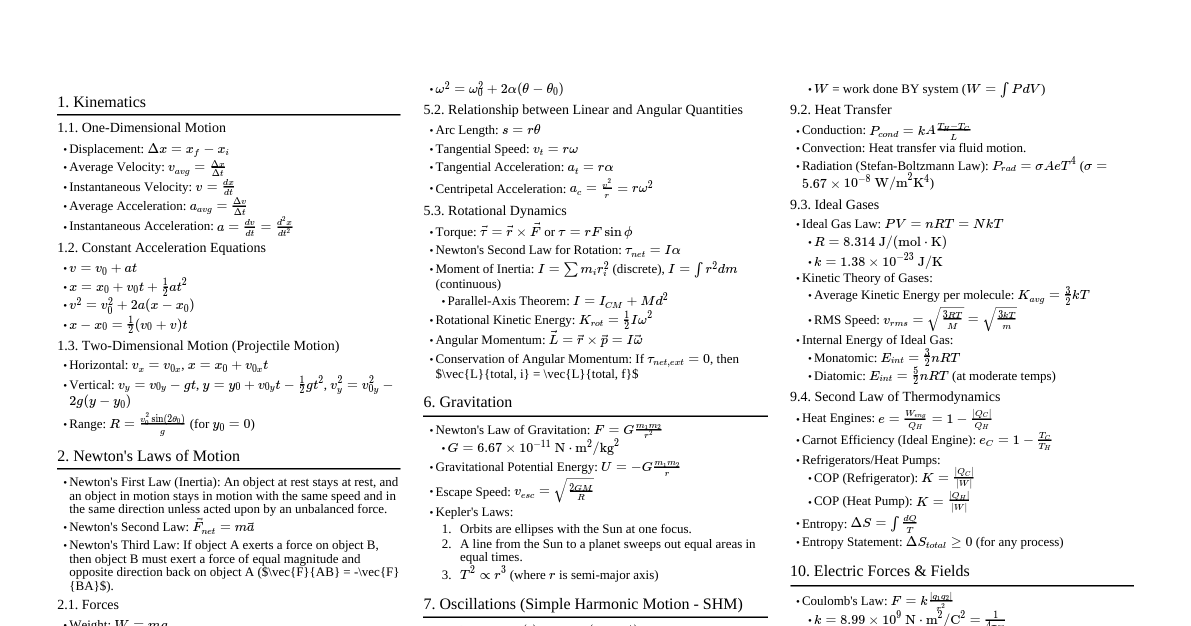
IT Virtualization Definition IT Virtualization: A process that makes physical computer hardware more effective and forms the basis for cloud computing. Uses software to create an abstraction layer over hardware, enabling multiple virtual computers (VMs) to split hardware elements from a single computer (processors, memory, storage). Each VM runs its own OS and acts like an autonomous computer, running on only a portion of the underlying hardware. Characteristics of IT Virtualization Increased Security: Transparently governs guest program execution, providing a safe, controlled environment. Execution Managed: Sharing, aggregation, emulation, and isolation are key features. Sharing: Enables separate computing environments on the same host, reducing active servers and energy consumption. Aggregation: Physical resources can be shared and individual hosts linked as a single virtual host. Emulation: Guest programs run within an emulated environment, allowing them to use features not present on the physical host. Isolation: VMs provide entirely separate environments, filtering guest activities and preventing dangerous operations against the host. Portability: VMs can be moved and executed safely on various virtual machines (hardware virtualization) or run on different virtual machines without recompilation (programming level virtualization). Types of Virtualization Server Virtualization: Masking of server resources (number, identity of physical servers, processors, OS) from server users. Example: VMware GSX Server converts computers into virtual machines. Desktop Virtualization: Virtualizing a workstation load rather than a server. Allows remote access to desktops, typically via a thin client. Examples: VMware Workstation, Microsoft's Terminal Services, Citrix's XenDesktop. Applications Virtualization: Tricks an application into believing it interacts directly with the OS, with a virtualization layer in between. Benefits: Runs legacy apps, cross-platform operations, prevents conflicts, allows multiple app instances. Limitations: Difficult for all programs (e.g., those requiring system drivers, 16-bit apps), anti-virus software, licensing issues. Network Virtualization: Network can be reconfigured on the fly without touching physical cables or devices. Integrates hardware, software, and network infrastructure into a single virtual network entity. Benefits: Customization of access (bandwidth throttling, QoS), consolidation of virtual networks. Storage Virtualization: Pooling of physical storage from multiple network devices into a single storage device. Benefits: Data migration without interrupting access, efficient storage device usage, centralized management. Disadvantages: Lack of standards, metadata management complexity, difficult backout from virtualized infrastructure. Common Virtualization Solutions Guest OS/Host OS Guest OS: An operating system secondary to the OS originally installed on a computer (host OS). Host OS: The original environment that manages the guest OS and physical resources. Hypervisors A firmware or low-level program that acts as a Virtual Machine Manager (VMM). Isolates OSs from the primary host machine. Type 1 Hypervisor (Bare-metal): Installed directly on physical server hardware (e.g., VMware ESXi, Citrix XenServer, Microsoft Hyper-V). Offers excellent performance and stability. Type 2 Hypervisor (Hosted): Runs within a physical host operating system (e.g., VMware Player, Parallels Desktop). Emulations The virtual machine simulates the hardware, making it independent of the host. Guest OS does not require modification. Bochs: Complete PC emulator of Intel x86 variant. QEMU: Open source machine emulator, can run OSs designed for one architecture on another. Uses dynamic translation, which can be slow unless integrated with KVM (qemu-kvm). Kernel-level Solutions Core component of an operating system, acts as a bridge between applications and hardware. Responsible for disk, task, and memory management. KVM (Kernel Virtual Machine): Linux kernel module providing a framework for virtualization, turning Linux into a hypervisor. User-Mode Linux (UML): Runs Linux inside Linux as a normal process, providing a virtual machine for testing. Solaris: Unix enterprise OS known for scalability. OpenVZ: Linux-system containerization platform, enables running Linux-based OSes in a single host system with a shared kernel. Benefits of Virtualization Resource Efficiency: Optimal use of hardware, reduced costs. Reduced Management Costs: Lower upgrade and resource costs, often automated by providers. Scalability & Flexibility: Meet changing business needs, rapid growth, data migration, upgrades, instant performance improvement. Server Consolidation: Replaces physical machines with virtual ones, reducing costs and physical space. Improved Security & Reliability: Helps avoid failures, memory corruption, offers improved security and reliability. Faster disaster recovery with snapshots and VM portability. Virtual Work-Stations: Allows multiple systems on a single computer, reduces hardware footprint. Development & Testing: Fast resource provisioning, no need for physical machines, easy setup of test environments and labs. Power Conservation: Energy-efficient, lower energy consumption rates. Faster Server Deployment: Near instantaneous capacity when a request comes. Service Commoditization: Separates applications into different environments, providing enterprise-class services at lower cost. Disadvantages of Virtualization Programs that Require Physical Hardware: Not suitable for applications needing specific physical hardware (e.g., dongles). Performance Quality Can Decrease: Can cause delays for RAM/CPU intensive applications due to layering. Testing is Critical: Requires thorough testing as it's not easily reversible. Unexpected Expenses: Initial setup can be complex and costly if not planned correctly. Data Can Be at Risk: Data hosted on third-party networks or shared hardware can be vulnerable if security solutions are inadequate. Quick Scalability is a Challenge: Scaling can be tedious and time-consuming, especially with third-party vendors. Unintended Server Sprawl: Easy creation of virtual servers can lead to an unmanageable number of VMs. Designing Virtualization Deployments: Needs Analysis Specifying Current and Expected User Requirements User requirements define what the computer needs to do (e.g., larger screen for better document viewing). Requirements can be job-related (e.g., scanning questionnaires) or health-related (e.g., larger screen for poor eyesight). Translating User Needs to Technical Specification Processor Load Assessment: Each physical CPU is abstracted into virtual CPUs, which time-share cycles. Hypervisor assigns one workload per vCPU. Fewer VMs per vCPU if more CPU cycles are needed. Storage Requirements: Storage virtualization pools physical storage into a single device. Different hypervisors use different file types (VDI, VHDX, VMDK, HDD). Operating System Requirements and Solution Needs: VMs require specific CPU, memory, and storage. Minimum requirements for KVM include 64-bit CPU with virtualization extensions, RAM, disk space, and network. Solution Needs: Interactivity, applications, development and testing, sandbox. Hardware Requirements Network Bandwidth: At least 1 GBps NIC recommended for smooth operation. Multiple NICs can be bonded for increased bandwidth and redundancy. Storage Capacity and Access Quality: Hard drive capacities are measured in GB or TB. Memory Requirements and Allocation (RAM): Temporary electronic storage. For systems up to 64 GB: RAM - 2 GB. For systems above 64 GB: RAM - (2 GiB + .5* (RAM/64)). KVM supports memory overcommitting. Compatibility: Components must be compatible (electrical voltages, communication). Modern systems are mostly compatible, but older hardware/software may cause issues. Selection of Most Appropriate and Cost-Effective Solution Server Consolidation and Containment: Eliminating "server sprawl" by deploying VMs to increase server utilization (5-15% to 60-80%). Test and Development Optimization: Rapidly provisioning test/dev servers, enhancing collaboration, standardizing environments. Business Continuity: Reducing cost and complexity of HA/DR solutions by encapsulating systems into single files. Enterprise Desktop: Securing unmanaged PCs/workstations without compromising user autonomy via security policy layering. Designing Virtual Machines and Networks for Security Nat Networks Used for setting up networks where VMs are NATed to access the internet and other networks. Host-only Networks Isolated networks where VMs can communicate with each other and the hypervisor machine, but not external networks. Implementing Virtualization Deployments Creating a Virtual Machine (Example: Windows 7 with MySQL) Install a virtual machine and Windows 7. Install MySQL and configure. Use regedit to navigate to HKEY_LOCAL_MACHINE\SYSTEM\SETUP . Add a new string value UnattendFile and set its data to a:\sysprep.inf . Launch sysprep.exe ( C:\Windows\System32\sysprep\ ). Under "System Cleanup Action", select "Enter System Out-of-Box Experience (OOBE)" and tick "Generalize". Under "Shutdown options", select "Shutdown". Backup the XML file using virsh dumpxml Win7_01 > /root/Win7.xml . Creating ISO Image (using WinCDEmu) Insert disc, open "Computer" folder. Right-click on drive icon, select "Create ISO image". Select file name and save. Creating Pre-existing Image Install snf-image-creator on host machine. Create and upload an OS image (e.g., clone from existing VM). Create VM from uploaded image. Testing an Environment: Compatibility for Hardware and Software Systems Network Infrastructure: Test physical and virtual network devices. Controller: Test centralized controller software (e.g., OpenFlow). Applications: Test various applications, including voice, video, enterprise apps, and security appliances. Test CPUs: Enable Intel VT-d or AMD IOMMU in BIOS. Check for CPU flags like 'svm' or 'vmx'. Memory (RAM): Ensure sufficient RAM for VMs and hypervisor. Test Storage: Factor in space for OS, SWAP, and VM disk usage. Documentation and Maintenance Installation Records: Document component parts in computers to identify unreliable components. Updated Manuals: Technical and user manuals should be updated with changes in hardware/software. Technical Manuals: Used by ICT professionals to understand and support systems. User Manuals: Easy to understand guides for end-users, regularly updated with tips. Monitoring Performance of the System Speed: Faster CPU improves VM performance. Memory Use: Sufficient physical memory is crucial for running high-capacity VMs. Accessibility: vSAN storage accessibility can change due to failures in the cluster. Impact on Host Environment: VM performance and resource usage impact host. Measuring Impact of Host Environment on Virtual Environment Cyclical Usage Patterns: Workloads can vary, impacting hosting requirements. High Availability and Disaster Recovery: Virtualization improves resiliency, but requires careful planning. Resource Reservations: Can limit environment density if not managed well. Affinities and Anti-Affinities: Separating or grouping workloads impacts capacity. Growth: Planning for future growth and maintaining "whitespace" is essential. Monitoring and Auditing Security IT auditor must understand VM technology, risks, infrastructure, access points, controls. Evaluate business need for physical-to-virtual migration. Apply principles and best practices from physical IT system audits to virtual systems. Evaluate precautionary measures based on situational awareness. Monitoring and Audit Points for Security of Virtual IT Systems Purpose of Moving from Physical to Virtual: Assess business need and compliance requirements. Risk Assessment: Evaluate expertise, training, procedures, single points of failure, security zones. Understanding Infrastructure and Controls: Partitions on different OSs/servers, controls over partitions, user access limits, naming conventions, deployment controls. Network Map of VM Environment: Location of systems (development, testing, production, business units), separation by sensitivity. Maintaining an Environment: Access Rights and Privilege Levels Install, remove, and update features, configure CD/DVD drives, sound cards, USB devices, graphic displays. Install VirtualBox following provided steps. Remove virtual machines and update features as needed. Virtual Disk Management Add secondary disks to VMs via Virtual Machine Manager. Ensuring Systems for Disaster Recovery and Business Continuity Virtualization simplifies disaster recovery by allowing VM backups to be restored quickly on new hardware. VMware survey indicates improved business continuity from virtualization. Testing: Usability, Performance, and Compatibility Usability Testing: Measures ease of use and user-friendliness. Performance Testing: Measures system performance under load. Applications may perform differently in virtualized environments. Performance bottlenecks can be magnified. Compatibility Testing: Checks software compatibility with different hardware, OSs, software, networks, browsers, devices, mobile platforms, and software versions. Types of Performance Tests Load Testing: Measures system performance as workload increases (concurrent users, transactions). Stress Testing: Measures system performance outside normal working conditions (e.g., until failure). Spike Testing: Evaluates performance when workloads rapidly increase. Endurance Testing (Soak Testing): Evaluates performance under normal workload over extended periods, checking for memory leaks. Scalability Testing: Determines how effectively software handles increasing workloads. Volume Testing (Flood Testing): Determines how efficiently software performs with large data amounts. Shortfalls and Solutions VM Sprawl: Unmanageable number of VMs. Solution: Monitoring lifecycles, growth patterns, using management tools. Complexity of Monitoring: Numerous layers in VM infrastructure. Solution: Proper software tool setup for accurate information capture. Lack of Visibility into Virtual Network Traffic: Difficult to enforce security policies. Solution: Address virtual network visibility. Offline and Dormant VMs: VMs not actively used. Virtualization Solutions Performance Management: Critical for shared resources. Prioritize resource usage, identify problem areas. Capacity Planning: Maintain sufficient capacity, plan for future growth, ensure correct resource allocation. VM Sprawl Identification: Monitor VM lifecycles and growth, identify unused/zombie VMs. Chargeback and Showback: Control growth and track resource consumption by allocating costs to individual VM usage. Storage I/O Bottleneck Identification: Identify and resolve performance bottlenecks in storage. Monitoring System and Data Security Firewalls: Inspect traffic between VMs, but traditional firewalls may not be tailored for virtualization. Administrator Access and Separation of Duties: Define granular access rights for server admins, separate authentication for guest OSs, separate duties for large environments. Network Security: Disconnect unused NICs, secure host platform, encrypt traffic. Auditing and Logging: Centralized logging for VM power events, hardware changes, login attempts. Regular audits of environment. Backups: Encrypt backup data streams, use access control lists, secure backups over network, regular full backups.